Domain-validated SSL certificate
Domain Validation (DV) certificates are SSL certificates that can be obtained very easily and very quickly. Thanks to simple verification and full automation, it is possible to obtain a new certificate in minutes and have a secure website one-two-three.
Even though domain SSL certificates are very cheap, they ensure quality https communication without any problems.
How domain validation works
After ordering, inserting of the certificate request (CSR) and payment, the SSL certificate is ordered from the certification authority, which immediately sends a validation email. After its confirmation, the authority issues the certificate. Validation can also be performed using FTP or DNS (see below).
The order
After ordering the SSL certificate and payment, the order is checked by the system and if everything is OK, the certificate is automatically ordered from the certification authority. Ordering a certificate from the authority is announced by email and the order will receive the status: PENDING
If you have received a confirmation of payment, but the order is still in the payment state and the order has not been sent to the certification authority, verify that the certificate request is submitted. Alternatively, simply generate a certificate request (CSR).
Verification by a Certification Authority
The validation of the certificate applicant is performed by the Certification Authority, ie it sends a validation e-mail, issues and sends the certificate.
Email validation:
The easiest way to validate is to verify the domain using an email sent to a pre-selected address, where the owner or administrator of the domain clicks on the link, where they then confirm the "Approve" certificate request. After that, the certificate is issued almost immediately.
Mailboxes to which a validation email can be sent:
- admin@example.net
- administrator@example.net
- webmaster@example.net
- hostmaster@example.net
- postmaster@example.net
The offered e-mails are set according to the rules of the CAB forum. The validation email must be created and functional. If you do not have one of these emails, you must create it and set it as an alias for a company e-mail, for example.
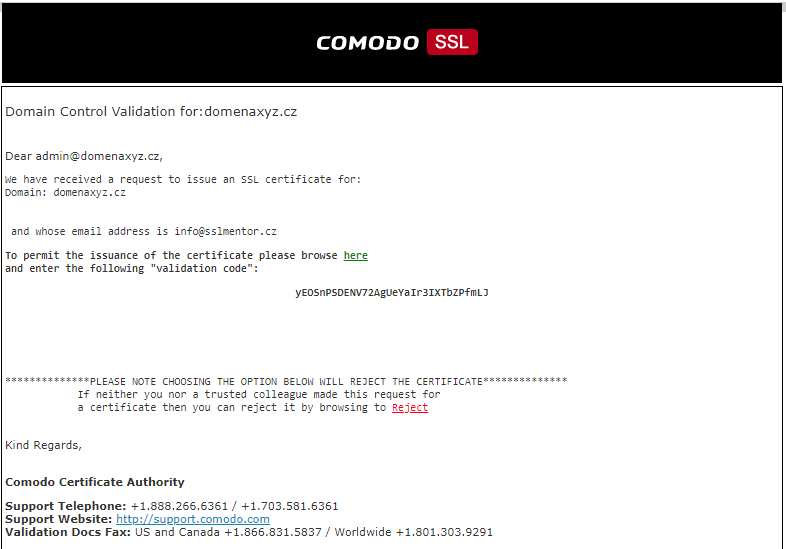
Sample of CA Sectigo validation email:
What to do if the validation email did not arrive?
The validation e-mail is sent directly to the certification authority immediately after ordering the certificate from the authority (CA Sectigo sends an e-mail from noreply_support@comodo.com). The e-mail address may not be available yet or you may need to change it to another 4 emails. Email forwarding settings may also fail or email may not be delivered due to a strict spam protection policy.
The validation email can be resent at any time before the certificate is issued. Forwarding is performed in the Control Panel: SSL Order Detail -> Order information -> Validation method: -> Edit -> Resend. Here it is also possible to change the e-mail and set another.
Important: If the validation email can't be received after multiple attempts, check the domain name for typos when ordering. It is also possible that your provider has anti-spam filters set up so that e-mails from a foreign authority are rejected. In this case, you must contact your email provider or consider using alternative validation.
Issuance of a certificate
As soon as the validation e-mail is confirmed, the certificate is issued within minutes and sent to the completed contact in the order.
The e-mail contains a certified public key and intermediate authority certificates, to ensure certificate trust. Everything is uploaded to the server together with the private key.
Alternative verification methods
If you can't verify the domain owner by email, there are two other ways to validate the domain.
File-Based Authentication (FTP validation)
The CA authenticates the domain using a TXT file located in the domain disk space. The publicly available file contains a text string (token) that must be uploaded to the /.well-known/pki-validation/ website directory. The certification authority verifies its existence and thus validates that the applicant has access to the domain and has the right to dispose of the domain. Each request always has its own text strings, which are listed next to the order detail and sent by email. The strings below are for illustration only.
Note: As of November 2021, it is not possible to verify WildCard SSL certificates using FTP validation. Only DNS.
Example of FTP validation of RapidSSL certificate
Name of file: fileauth.txt
Path to the file: http://example.net/.well-known/pki-validation/fileauth.txt
Content (token):
8CC79447A5MTg4MzY1MA2#!cm5ywz5m1lzoyfp2xhy7
The text file contains only the token, without any other information.
Example of FTP validation of Sectigo PositiveSSL certificate
Name of file: 048B0565E245687S52C7801EA7D4B954F3.txt
Path to the file: http://example.net/.well-known/pki-validation/048B0565E245687S52C7801EA7D4B954F3.txt
Content:
141A63FD5637E4524954SDAB4B2C0B4DBD0CCFABD5379DF821F5F01B3B69116993
COMODOCA.COM
t0211231001361667854
All entered parameters must be on separate lines!
Important: The authentication file must be accessible at an address without "www". Even in the case of a certificate request for a domain with "www", for example www.example.net.
Verification of whether the record is available is performed by a simple check by entering the address into the browser, where the validation information must be displayed.
DNS validation
Domain DNS records are usually set up by your hosting provider or domain registrar. The certification authority generates a unique string, which is inserted into the DNS as a TXT record, or the CNAME is set. As new DNS content spreads, the CA checks the record and issues a certificate to the domain if it is OK.
Example of DNS validation using TXT record
DNS TXT record: d3pyrjg65d8hh1bv0tgr4bx890yksq8j
Example of DNS validation using a CNAME record
DNS CNAME record: _cfd00c1ec2d56372b27b9562f5da83d0.example.net CNAME
cb3a889855882c6518c0ac959be30067.e8349bfb8ec9a0334864d9bf350a1188.t0119001001421510849.comodoca.com
Important: Even when requesting a certificate for the domain www.example.net, the TXT record must be available in DNS on the domain without "www".
Verification of whether the record is available can be found online using digwebinterface.com nebo whatsmydns.net.
Where next?
Back to Help
Found an error or don't understand something? Write us!






